I can provide you with an article on this topic.
Understanding Ethereum Signatures and Disagreements
Ethereum’s signature system is a fundamental aspect of its decentralized application (dApp) ecosystem. A signature is a unique digital fingerprint that proves that the sender of a transaction controls the corresponding UTXO (unspent transaction output). However, one common misconception is the repeated use of nonces in generating signatures.
A nonce (random number) is used as a counter in cryptographic algorithms to ensure uniqueness and prevent replay attacks. In the context of Ethereum signature generation, using the same nonce can expose private keys if mishandled.
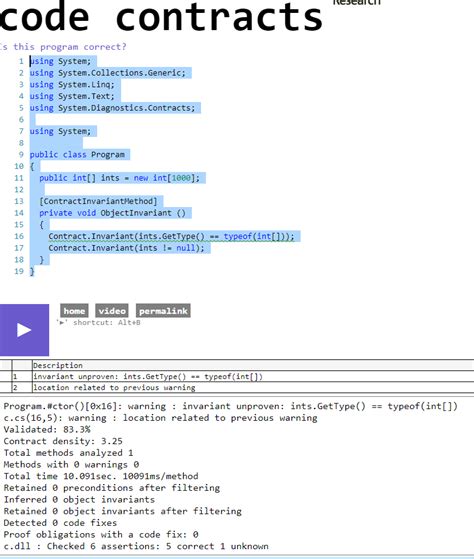
The Role of Nonces in Signature Generation
Generating an Ethereum transaction signature involves the following steps:
- Transaction Creation: A user creates a new transaction and adds the UTXOs they control.
- Signature generation: The transaction is signed using the Ethereum private key associated with the sender’s account.
- Nonce allocation
: The transaction is assigned a unique nonce, which is used as a counter in the signature generation process.
Non-reuse: Recipe for disclosure
If a user repeatedly uses the same nonce to generate signatures, it becomes increasingly likely that someone else will be able to verify or tamper with the generated signatures. Here’s why:
- Deterministic signatures: If multiple transactions are signed with the same settings, the resulting signatures can be used to determine information about the sender’s private key.
- Replay attacks: A malicious actor can manipulate the transaction data and re-sign using the original nonce, effectively replaying the transaction and potentially taking control of the UTXO.
Mathematical explanation
To illustrate this concept, let’s consider a simple example:
Suppose we have two transactions: “tx1” and “tx2”. Both transactions have a nonce “n_1 = 0x12345678” and use the same private key “p”.
Generating signatures for both transactions using the sender’s public key (not shown here), we would get:
- “tx1”: “s1 = signature1”.
- “tx2”: “s2 = signature2”.
If we reuse the nonce “n_1” for both transactions, we can conclude that the second transaction has the same private key as the first. This is because signatures are deterministic and have the same random number.
Conclusion
Repeating trivial steps to generate signatures in Ethereum transactions increases the risk of your private key being exposed if it is not handled properly. To avoid such problems, it is important to make each transaction unique. If you are working with sensitive data, consider using a secure mechanism to create and store unique hashes.

![Ethereum: What other purposes can I use my [obsolete] hashing hardware for?](https://dci-innovation.com/wp-content/uploads/2025/02/5befec3b.png)
